NewsList
-
 2025/12/25
info
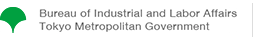
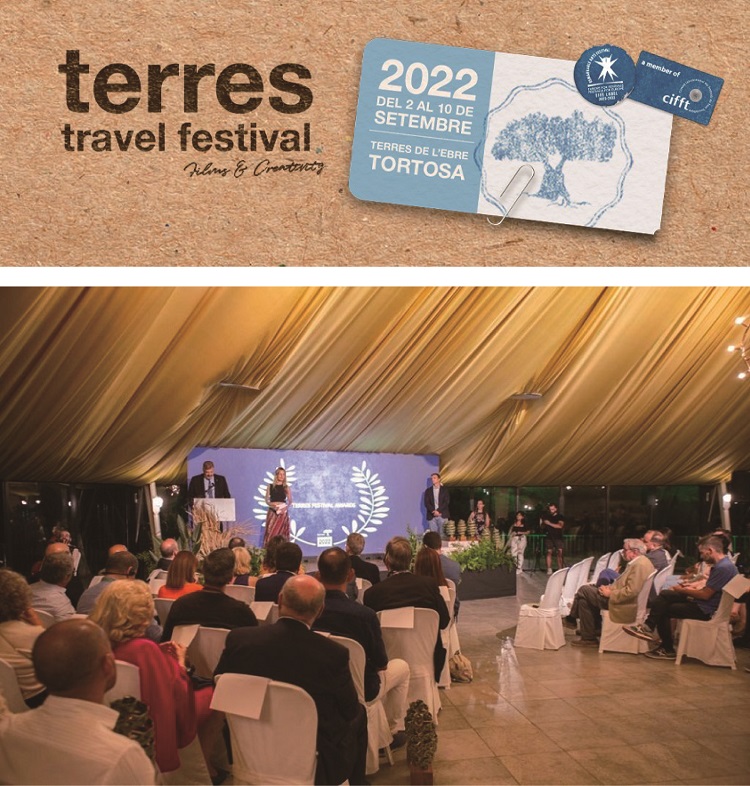
Tokyo Film Commission’s promotional film “What shall I shoot in Tokyo?” won a gold award at Terres Travel Festival 2022
2025/12/25
info
Tokyo Film Commission’s promotional film “What shall I shoot in Tokyo?” won a gold award at Terres Travel Festival 2022
-
 2021/10/22
info
Tokyo Film Commission-supported drama “TOKYO VICE” to air and stream in US and Japan
2021/10/22
info
Tokyo Film Commission-supported drama “TOKYO VICE” to air and stream in US and Japan
- 2021/01/20 info Response to the Declaration of a State of Emergency
-
 2021/01/05
info
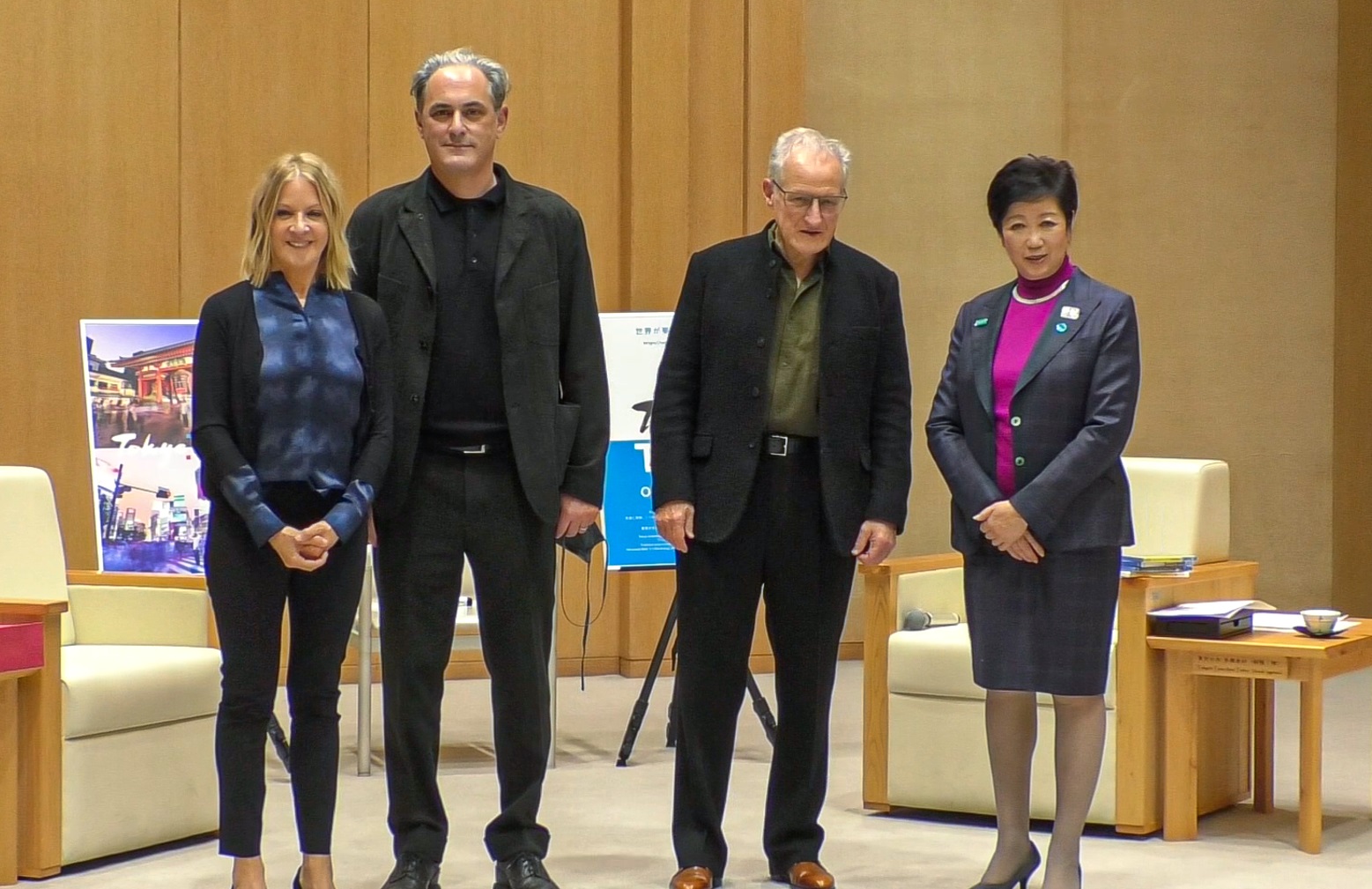
“TOKYO VICE” Director Michael Mann pays a courtesy call on Tokyo Governor Yuriko Koike
2021/01/05
info
“TOKYO VICE” Director Michael Mann pays a courtesy call on Tokyo Governor Yuriko Koike
-
 2021/01/05
info
“MOVIE WALKER PRESS” features Tokyo Location Box
2021/01/05
info
“MOVIE WALKER PRESS” features Tokyo Location Box